原文出處:https://thehackernews.com/2018/08/ghostscript-postscript-vulnerability.html
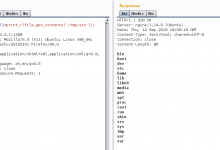
Google Project Zero's security researcher has discovered a critical remote code execution (RCE) vulnerability in Ghostscript—an open source interpreter for Adobe Systems' PostScript and PDF page description languages.
Written entirely in C, Ghostscript is a package of software that runs on different platforms, including Windows, macOS, and a wide variety of Unix systems, offering software the ability to convert PostScript language files (or EPS) to many raster formats, such as PDF, XPS, PCL or PXL.
A lot of popular PDF and image editing software, including ImageMagick and GIMP, use Ghostscript library to parse the content and convert file formats.
文章圖片來源:https://thehackernews.com/2018/08/ghostscript-postscript-vulnerability.html
前言引用來源:https://thehackernews.com/2018/08/ghostscript-postscript-vulnerability.html
-------------------
如果你認同支持我們每日分享的文章的話,請幫我們按個讚並且點擊追蹤「搶先看」,這樣就可以快速獲得最新消息囉!
您的分享及點讚,是我們最大的動力來源。
https://www.facebook.com/LonelyPoPo/