原文地址:https://blog.ripstech.com/2019/wordpress-image-remote-code-execution/
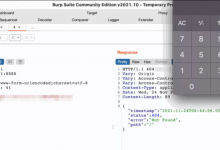
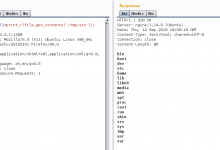
This blog post details how a combination of a Path Traversal and Local File Inclusion vulnerability lead to Remote Code Execution in the WordPress core. The vulnerability remained uncovered in the WordPress core for over 6 years.
前言引用來源:https://blog.ripstech.com/2019/wordpress-image-remote-code-execution/
文章圖片來源:https://blog.ripstech.com/2019/wordpress-image-remote-code-execution/
-------------------
如果你認同我們每日分享的文章,請幫我們按個讚並且點擊追蹤「搶先看」,讓我們提供最新消息給您!您的分享及點讚,是我們持續推廣資訊安全最大的動力來源。
https://www.facebook.com/LonelyPoPo/